Sanchar Saathi: The Government’s New Tool To Protect Your Mobile Identity
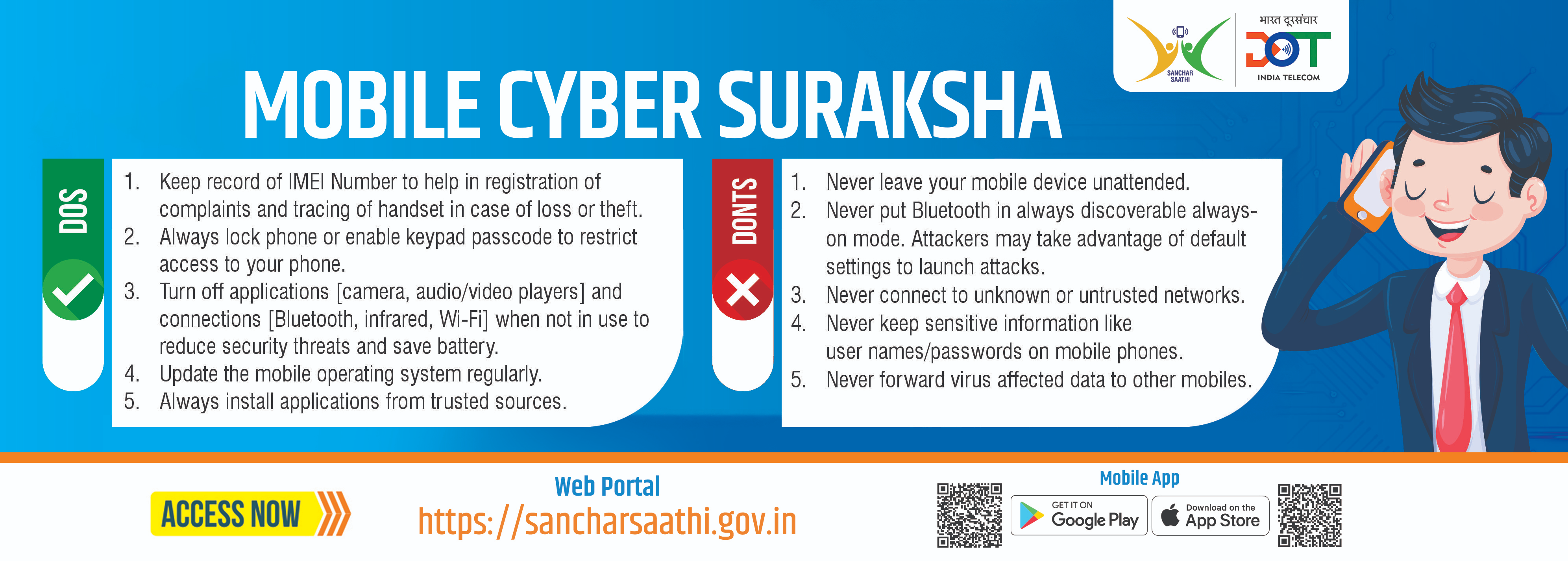
Digital fraud in India has grown aggressively over the past few years, and most scams start with one simple point of failure: the victim’s mobile number. To tackle this, the Department of Telecommunications (DoT) launched Sanchar Saathi, a unified platform designed to help citizens secure their mobile connections, detect fraud, and report misuse.

For mobile users, who rely heavily on online services and multiple connected devices, understanding this tool isn’t optional anymore. It is becoming one of the most important digital safety platforms in India.
What Exactly Is Sanchar Saathi?
Sanchar Saathi is a government-backed portal and mobile app that gives users control and visibility over all mobile numbers issued in their name.
It brings together multiple cybersecurity systems built by the DoT, including:
- CEIR (Central Equipment Identity Register)
- TAFCOP (Telecom Analytics for Fraud Management and Consumer Protection)
- KYC-based fraud detection tools
Instead of visiting your telecom provider or dealing with long customer service loops, Sanchar Saathi centralizes everything in one place.

Key Features That Actually Matter
1. Find All Mobile Numbers Issued in Your Name
Most users don’t realize how many SIMs are linked to their ID documents. This is exactly how many frauds happen.
Sanchar Saathi shows a list of all numbers registered with your Aadhaar-linked identity.
You can instantly:
- Identify unknown or suspicious numbers
- Flag and report unauthorized connections
- Request disconnection of fraudulent SIMs
2. Block Your Lost or Stolen Phone
Using the CEIR system, you can permanently block your lost phone using its IMEI number.
Once blocked:
- No SIM will work in that device
- The phone becomes useless for thieves
- You receive updates once it’s traced or recovered
This feature alone has shut down a huge chunk of device theft operations.
3. Track IMEI Changes and Clone Devices
If someone clones your IMEI or tampers with your device identity, Sanchar Saathi notifies you.
This is especially critical for users who frequently travel or switch devices.
4. Protect Yourself From SIM Swap Fraud
The app alerts you about SIM changes and reactivations connected to your number.
SIM swap scams are used to break into:
- UPI
- Banking apps
- Email accounts.
- These alerts act as early warning signs.
5. Disable Misused Mobile Numbers
If someone is using your identity to run scams, you can lodge a request to shut those connections down.
How To Use Sanchar Saathi (Quick Steps)
- Visit https://sancharsaathi.gov.in or download the app.
- Log in using your mobile number and OTP.
- Check the list of SIMs linked to your identity.
- Report and block numbers you don’t recognize.
- Use CEIR to block a lost device using its IMEI.
- Track status updates directly from the dashboard.
Conclusion
Sanchar Saathi is not just another government app; it is a practical safety shield for every smartphone user in India.
With rising SIM fraud, digital impersonation, and device theft, tools like this have become essential.

Follow me ➡️@TechieGuy for more such amazing content 🚀.
Please sign in
Login and share

























